So, you are connecting to another tenant in Teams and you get an MFA prompt. Maybe that is unexpected, or it is not because you know the other tenant requires MFA for guests. But the prompt shows a branding from your Home Tenant. You might not be used to MFA prompts from your Home Tenant because you always log in from a compliant device. Which tenant is it now that is prompting you for MFA?
In this article, the expression “Home Tenant” is used to denote the tenant where the Azure AD account of the user resides. The expression “Inviting Tenant” is used for the tenant where the B2B Guest account of the user resides.
For the sake of demonstration, let’s assume you use a new in-private window or guest window in a browser (so there are no tokens in cookies and there is no access to the Primary Refresh Token that could get in the way). The Home Tenant requires MFA for the user and the Inviting Tenant requires MFA for guests. Then you will have a logon experience as shown in this video:
There are two MFA prompts. The first MFA prompt at 00:27 comes from your Home Tenant as you are authenticating to Teams in your Home Tenant. It has the branding from the Home Tenant and the notification in the authenticator app looks like this:

The second MFA prompt at 01:00 is from the Inviting Tenant as you are authenticating to Teams in the Inviting Tenant.
Noted in August 2020, but the change in behavior might have been made some time before: the background image is now from the resource tenant, while the banner logo in the dialog box is from the home tenant.
but the notification in the authenticator apps looks different:

If you are using the authenticator app, then this is how you can tell the difference: you will see the B2B guest account syntax in the notification if the MFA prompt comes from the Inviting Tenant.
Obviously, for such a logon experience as shown in the video, you must have registered with MFA in both tenants at some point in time in the past. Note that this are two separate and independent MFA registrations! Here is how you can navigate to the MFA settings in the Inviting Tenant:
In a browser, connect to https://myapps.microsoft.com and authenticate normally with your Home Tenant credentials (or use a browser session that is already authenticated).
August 2020: myapps.microsoft.com redirects to myapplications.microsoft.com by default. To navigate as described below you will have to click on ‘Leave new experience’ from the dialog of the account object in the upper right corner.
Click on the User Icon and choose “Profile” or choose the settings symbol next to Organizations.

The next page shows your Home Tenant and all the other Tenants where you have a guest account. Click on “Sign in to leave organization” for the Inviting Tenant in question.

You should be getting an MFA prompt as you sign in to the Inviting Tenant. If you click on the user icon, you see that you are logged on to the Inviting Tenant now.
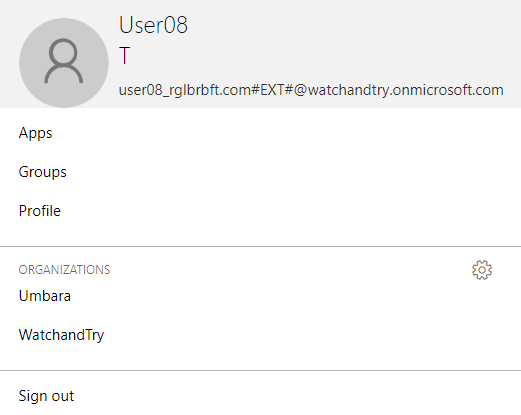
If you choose “Profile”, you can also see that you are logged on to the Inviting Tenant as it offers you to “Leave Organization”. Obviously, this is not what you want to do at this point as it deletes your guest account in the Inviting Tenant.

Instead, choose “Additional security verification” as this takes you to your guest account’s MFA settings in the Inviting Tenant.

That said, you can set up a different authentication method for the Inviting Tenant. For example, use the Authenticator app in your Home Tenant and use phone call or text message in the Inviting Tenant. That will also let you distinguish between MFA prompts from the two tenants quite easily.
On the side: some people, myself included, believe that two or more MFA registrations is too confusing for users. We therefore recommend to exclude guest users from any and all MFA requirements. For guests: manage authorization, not authentication!

