In this article, the expression “Home Tenant” is used to denote the tenant where the Azure AD account of the user resides. The expression “Inviting Tenant” is used for the tenant where the B2B Guest account of the user resides.
Find the Tenant ID
Now this is about finding the Tenant ID of the Inviting Tenant.
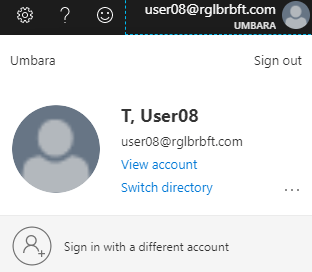
You can open the Azure Portal, logging on as the Azure AD user in the Home Tenant. Even if you are not allowed to navigate, which is likely, you can click on “Switch Directory” in the upper right corner and read the IDs of all tenants in which you are a guest.
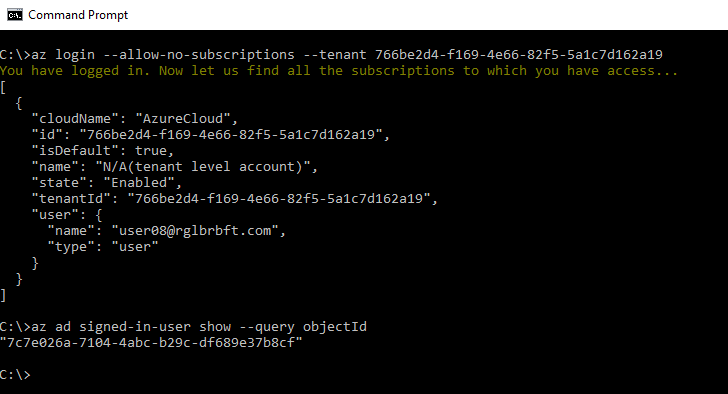
Another way to find the Inviting Tenant’s ID is Azure CLI. Use the command az login --allow-no-subscriptions to log on to Azure without connecting to any subscription. Your default browser opens to start an interactive login dialog. Log on using the credentials from your Home Tenant. The logon dialog will include an MFA prompt from your Home Tenant, if your Home Tenant requires MFA for you. Right after login you get a list that includes your Home Tenant (“isDefault”: true) and that includes one entry for every Inviting Tenant (“isDefault”: false) where you have a guest account.

Instead of a list entry you might get an error message for a given Inviting Tenant, this is the case if the Inviting Tenant requires MFA for you to sign in. No matter if you get a valid list entry or an error message, the Tenant ID is displayed in either case. If you have guest accounts in many tenants, it might be difficult to understand which Tenant ID belongs to which tenant. The easiest way to find out is to compare the Tenant IDs from the Azure CLI to the list you see in Azure Portal when you click on “Switch Directory”.
On the side: in this Azure CLI session, you can use the command az ad signed-in-user show --query objectId to get the Object ID of the Azure AD account in the Home Tenant. But there are easier methods for that.
Find the Object ID
This is about finding the Object ID of the guest account in the Inviting Tenant.
You can use Azure CLI to do that. Use the command az login --allow-no-subscriptions --tenant <Tenant ID>. The default browser opens and shows the branding from the Inviting Tenant when asking for the user name.

Ignore the branding and enter the user name from the Home Tenant. When displaying the prompt for the password, the branding from your Home Tenant is shown. The background picture is still from the branding of the Inviting Tenant.

If you find the branding story confusing so far, wait until we talk about MFA! Directly logging in to the Inviting Tenant bypasses Conditional Access in the Home Tenant:

So you never get an MFA prompt from you Home Tenant when logging in directly to the Inviting Tenant. However, you might still get an MFA prompt at this point: if the Inviting Tenant requires MFA for your guest account. While it is the Inviting Tenant that prompts you for MFA, note that the prompt branding and the background branding is from your Home Tenant.

Let’s hope the Inviting Tenant does not require MFA for a guest login. Anyway, now you are logged on with your guest account in the Inviting Tenant. You can now run the command az ad signed-in-user show --query objectId, which will display the Object ID of your guest account.
One final word
about the default browser that opens during the interactive az login. If you have an Azure AD joined Windows 10 device or a Hybrid Azure AD joined Windows 10 device and if you use a default browser that can access your Primary Refresh Token, then you can only interactively logon to Azure CLI with the currently logged on Windows user. This is fine if that’s the account you are looking at anyway.
If not, you have to use a workaround. What you can do is to temporarily set up a default browser that cannot access the Primary Refresh Token; Firefox is a good choice. With Firefox as default browser, you can interactively logon using az login with any Azure AD account.

